It can be easy to dismiss social media security as a chore to save for another day. Getting hacked is serious business though, and you could find your online identity stolen, your precious photos erased and your devices inaccessible. Fear not! We’ve put together some simple but effective ways of keeping the hackers out.
Of course, on the wilds of the Web no protection is ever 100 percent guaranteed, but you can certainly minimize the risk and sleep more soundly at night knowing that you’ve done what you can. If you’ve got any security tips of your own, we’d love to hear them in the discussion below.
Do the two-step
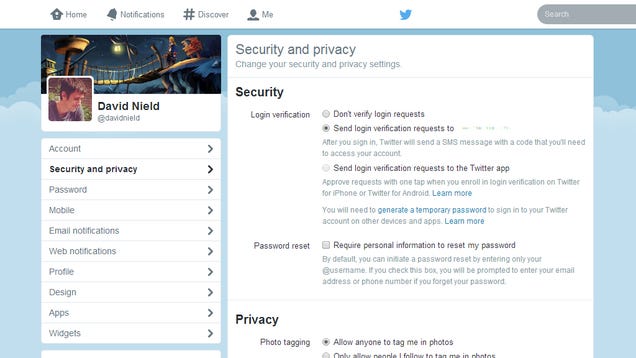
Most of the big social networks now offer some form of two-step verification, which adds an extra step to the login process when you sign in on a new computer or device. Essentially, it means that potential bad guys need more than just your username and password to get at your accounts on a browser or phone that you’ve not used before. The extra code that’s required is typically sent via SMS, or generated through a mobile app.
Usually, you’ll only need to go through the extra step once on each computer or device that you use. It’s simple, effective, and should be your very first stop on the security tour.
 Expand
Expand
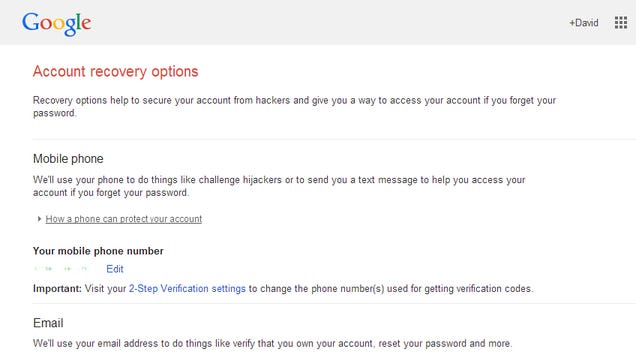
On Facebook, head to the Login Approvals section under the Security page on the Settings screen; on Twitter, the option you’re looking for is called Login verification under the Security and privacy page of your settings. It’s also available for Gmail and Google (choose Security then 2-step Verification from your Google Account page), Tumblr (Account>>Security>>Two-factor authentication), Dropbox (Settings>>Security>>Two-step verification) and many other major services.
Whatever the name given to the feature, it’s worth switching on wherever it’s available. It’s not foolproof, but it adds an extra layer of protection should your username and password get out into the wild.
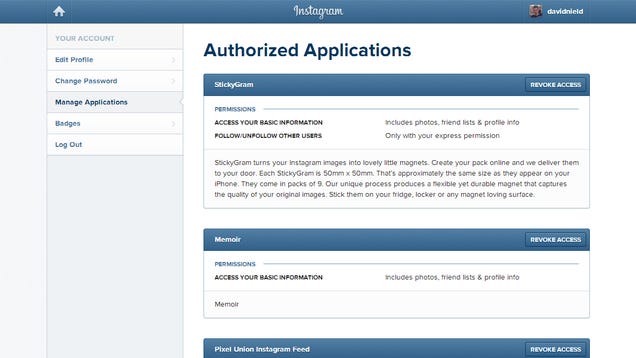
Disconnect third-party apps
Chances are that your Facebook, Instagram, Twitter and Google accounts are linked to all kinds of third-party services and apps that you’ve signed up for down the years. These extra apps may well be legit and useful, but each one can be used as a backdoor into your social media accounts. With this in mind, it’s worth running a regular audit of all of the services you have connected and removing the ones you no longer use or which are no longer updated. Even if the apps themselves are genuine, their databases might fall prey to someone who isn’t, and the less exposed you are the better.
 Expand
Expand
Again, the relevant screen will be in a different place and given a different label depending on the account in question, but you should be able to find it without too much digging around. On Instagram’s Web interface, for example, click the Edit Profile link under your avatar and then choose Manage Applications. Select the Revoke Access option next to any service you don’t recognize or no longer use. If you make a mistake, you can always add the app again in the future, and it’s best to err on the side of caution.
Avoid phishing trips
You’d be surprised at the number of large-scale hacks caused by people clicking on links that they shouldn’t have. It’s been said many times before but it apparently needs repeating: don’t click on links that arrive in your inbox or over instant messenger programs unless you’re absolutely sure they’re genuine (if you’ve just created an account or just reset your password perhaps). If you have any doubt, go directly to the site and login rather than relying on a link that has popped up on screen.
 Expand
Expand
Fortunately for the easily fooled, most modern email clients and Web browsers do a decent job of spotting these phishing attacks. You should always make sure you are running the very latest versions of your favorite email and browser programs to take advantage of the newest security and anti-phishing features. The green padlock symbol sported by most browsers when you’re on a secure site is one of the signs you should look for whenever you’re being asked to log in again.
Lock up your devices
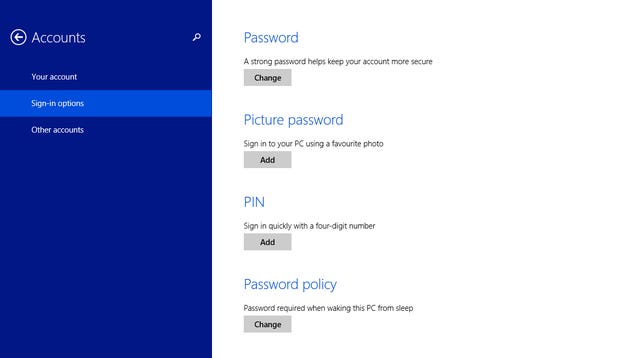
Once you’ve logged into Facebook or Twitter on your laptop, you’ll want to set the machine as a trusted device so you don’t need to keep repeating the process. The same goes for your phone, tablet and other computers you’re using. This makes it easy to get a quick social media fix whenever you like, but it also leaves the door wide open to anyone who can gain access to your laptop or phone.
Make sure that each of your trusted devices is protected by at least a password or passcode, and that they are set to lock or hibernate after a short period of inactivity. Whether it’s the fingerprint lock on the iPhone or the picture password on Windows, make sure a layer of security is in place. Otherwise, anyone wandering up to your laptop or picking up your phone on the subway can start posting as you.
 Expand
Expand
This should be common sense, but some estimates say as many as 60 percent of us don’t bother with a passcode. Even if you only have one user account on your computer and you’re normally the only person who accesses it, you should always have a password in place—you’ll be glad you did after someone swipes your laptop at the coffee shop.
Passwords
We’ve all heard the mantra that passwords should be long and complex, but hack after hack shows that most of us are still using the likes of “123456” and “password” as the keys to our kingdom. Mix up your passwords with numbers, special characters and a mixture of uppercase and lowercase letters and they are much more difficult to crack for human hackers and automated bots alike. If you can’t remember all of the login details for all of your accounts, then use a password manager such as 1Password or LastPass for the job.
 Expand
Expand
Tempting though it is, don’t use the same password for all of the sites and services you use—the least well-protected of these can then be exploited to gain access to everything else.
It’s like having the same master key for your car, safe, and house. Even just changing around a few letters in each password (adding FB! at the end for Facebook, perhaps, or TW! for Twitter) can make a big difference. While we’re on the topic, review the password reset procedures for the social networks you’re signed up for as well. This will usually be in the form of an email address you can send a reset link to; make sure this is a current email address and one that’s well-protected.
If there are any other security measures offered for recovering a hacked account, activate them. Facebook has a Trusted Contacts feature you might not have seen, for example, that lets you can list a few close friends who will verify your identity if you ever find yourself locked out.
Again, there’s not totally foolproof way to lock down your social media presence. But the harder a target you make yourself, the better your chances are of keeping your identity to yourself.